Perfect Privacy setzt sich seit 2008 für die Privatsphäre und Anonymität seiner Kunden ein und ist seit Beginn einer der sichersten VPN-Anbieter weltweit. Der Schutz Ihrer Privatsphäre liegt uns am Herzen – deshalb protokollieren wir keine Nutzeraktivitäten.
Sie können frei zwischen all unseren schnellen VPN-Servern wählen. Diese sind rund um die Welt verteilt, darunter beliebte Standorte wie Schweden, Russland, Island, Hong Kong und die Niederlande. Die meisten haben IPv6 Adressen und eine Bandbreite von 1000 Mbit/s.
Wir vertrauen auf Open-Source-Software und entwickeln alle Privacy-Lösungen in-house ohne Drittanbieter. Zur Verschlüsselung nutzen wir bewährte und sichere Industriestandards wie beispielsweise OpenVPN (AES 256Bit) und IPsec, die unter allen gängigen Betriebssystemen einsetzbar sind.
Unser Entwickler-Team erforscht für Sie laufend neue Technologien, um sinnvolle Features wie z.B. NeuroRouting und TrackStop, die dem Komfort und der Sicherheit dienen, in unser VPN zu integrieren. Außerdem geben wir intern und extern regelmäßig Code-Audits in Auftrag um mögliche Sicherheitslücken aufzudecken und teilen diese auch anderen VPN-Anbietern mit, um das Internet für alle Nutzer sicherer zu machen.
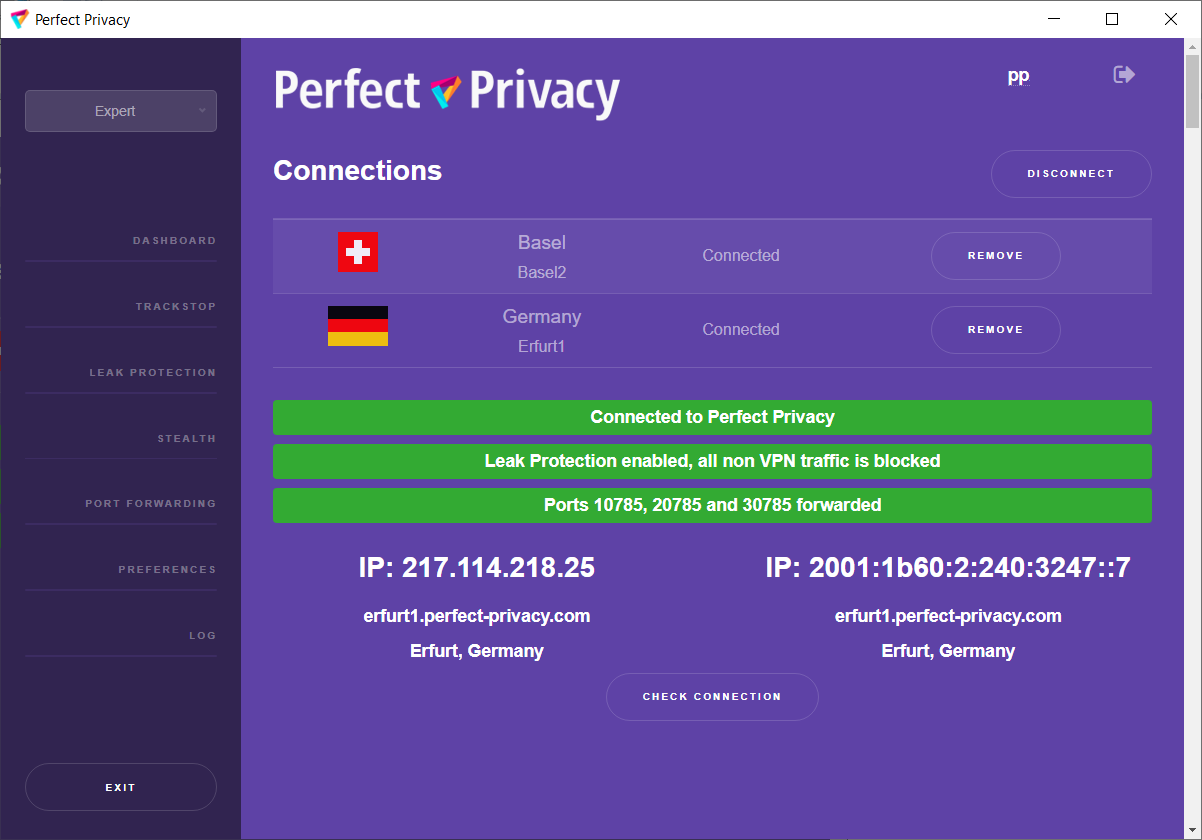
Zudem stellen wir Ihnen auf das Perfect Privacy VPN zugeschnittene VPN-Client-Software für verschiedene Betriebssysteme zur Verfügung.
Auf unserer Warrant Canary Erklärung können Sie jederzeit erkennen dass wir unabhängig agieren.
| Keine Speicherung von Log-Dateien | |
| Für alle Ihre Geräte | |
| Kaskadierung über mehrere VPN-Server | |
| Konfigurierbare Port-Weiterleitungen | |
| Keine Traffic-Begrenzung | |
| Bis zu 10.000 Mbit/s Bandbreite | |
| Einfach benutzbare Client-Software | |
| Support via E-Mail, Forum und TeamViewer | |
| Wahlweise über OpenVPN, IPsec/IKEv2, SSH2-Tunnel oder PPTP | |
| IPv6 Support | |
| TrackStop™ | |
| Stealth VPN Technologie | |
| NeuroRouting™ | |
| 7 Tage Geld-zurück-Garantie |
| Kaskadierung über bis zu 4 VPN Server. Freie Serverauswahl | |
| Automatische Einrichtung Ihrer Windows Firewall | |
| DNS-Leak-Schutz | |
| 8 Port-Weiterleitungen inklusive (z.B. für BitTorrent) | |
| Serverwechsel so oft Sie mögen | |
| Ping-Zeiten zu den Servern in Echtzeit überprüfen |
Für weitere Systeme, Router oder individuelle Konfigurationen finden Sie Schritt-für-Schritt Anleitungen in unserem Anleitungsbereich.