
Windows-users: Download the Perfect Privacy VPN Manager here. Start the installation by double-clicking the downloaded file. If you need step-by-step instructions for the installation, you can find it in the Windows section of our tutorial section.
Thank you for choosing Perfect Privacy. On this page, we want to show you the necessary steps after getting your login credentials so that you can enjoy a fully encrypted internet connection within a few minutes.
Note: This document is for Windows users as it explains the setup of a VPN connection with the Perfect Privacy VPN Manager.
If you are not using Windows, please visit our Tutorial Section where you can find detailed step-by-step instructions for setting up VPN on Linux, macOS, iOS, and Android.

Windows-users: Download the Perfect Privacy VPN Manager here. Start the installation by double-clicking the downloaded file. If you need step-by-step instructions for the installation, you can find it in the Windows section of our tutorial section.
Once the installation has finished, you can start the software. Click on "Perfect Privacy App" in the Windows Start Menu or on your desktop.
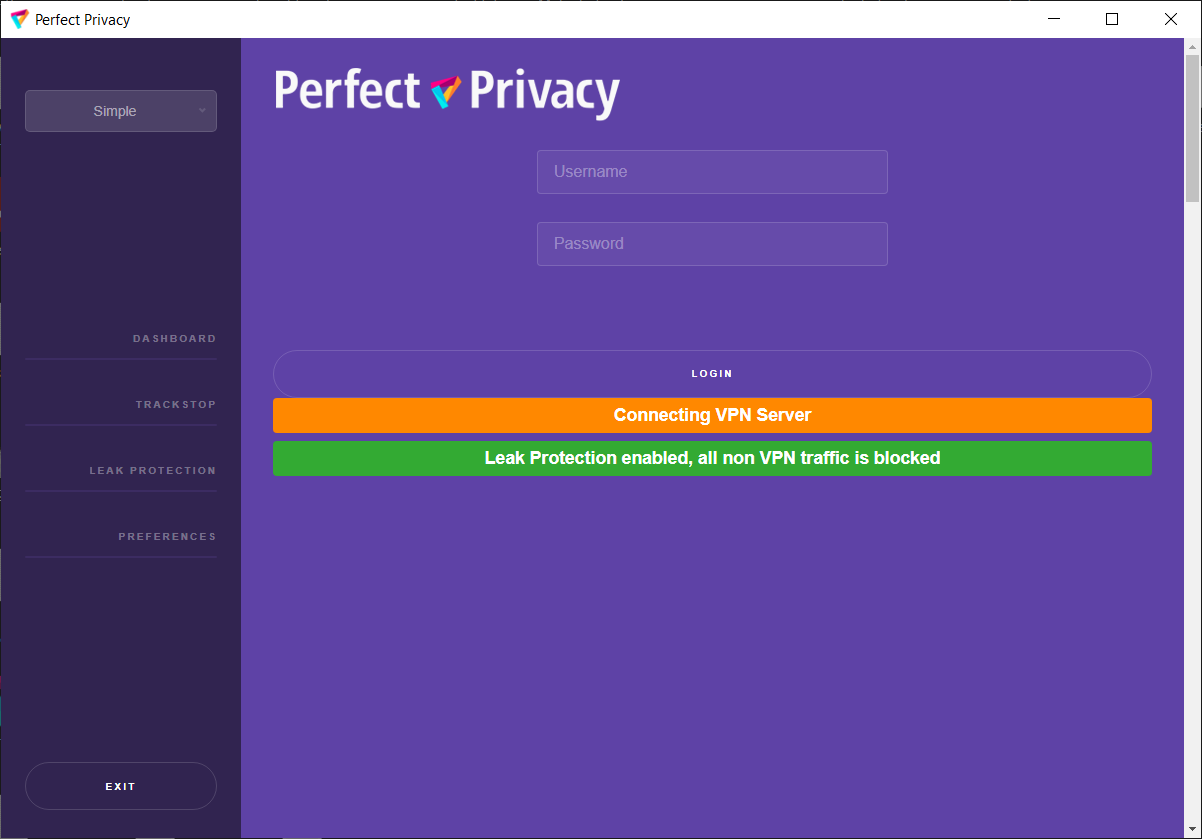
The program will automatically open the dashboard, where you must first enter your Perfect Privacy credentials once. Once this is done, you can click "Log In".
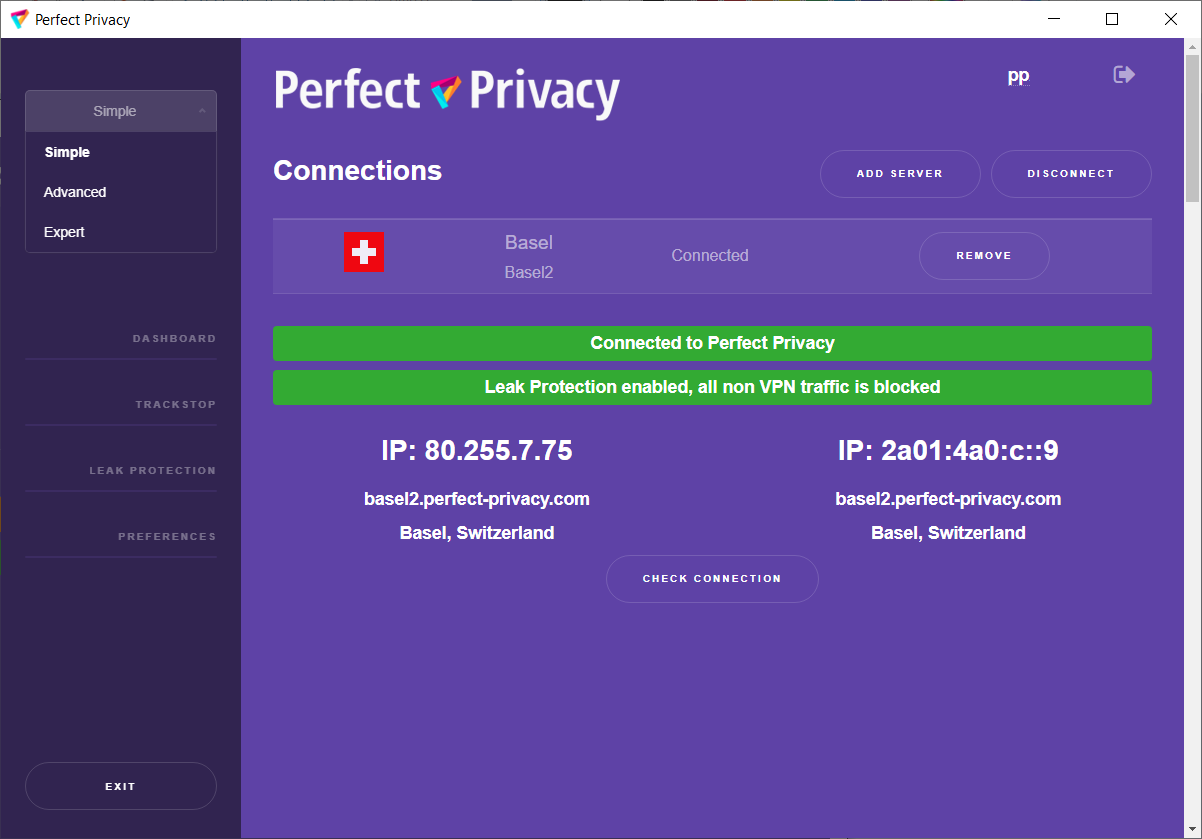
You will now be automatically connected to a preset VPN server. However, you can choose another server at any time by clicking "Remove" and then "Add Server" to choose another one. When "Connected to Perfect Privacy" appears in the green bar in the dashboard, you are connected.
From now on, all your Internet traffic should be routed over the secured Perfect Privacy VPN network. Should you wish to terminate the VPN connection, simply click on "Disconnect".
Perfect Privacy VPN Manager offers a wide range of functions and settings to customize the use of a secured tunnel.
After the first installation you are in "Simple" mode. There we have preset the most important settings for your security. In "Adavnced" you have more setting options and in "Expert" you can use the full scope. If you are not sure or you have misconfigured, you can switch back to "Simple". Then all settings you made in "Advanced" or "Expert" will be reset.
For a detailed description of these and more functionality, please read our Windows software page. For a complete reference of all options and functionality, please refer to the manual corresponding to your version of Windows in our documentation.