If you cannot establish a VPN connection using either the regular OpenVPN or IPsec/IKEv2 profiles, you are probably on a network that blocks VPN connections. In this case Stealth VPN helps to break out of this restrictive network anyway. Using the following step-by-step instructions, you can establish an OpenVPN connection with Tunnelblick, which is obfuscated with obfsproxy. For a simpler solution, use Perfect Privacy's VPN software.
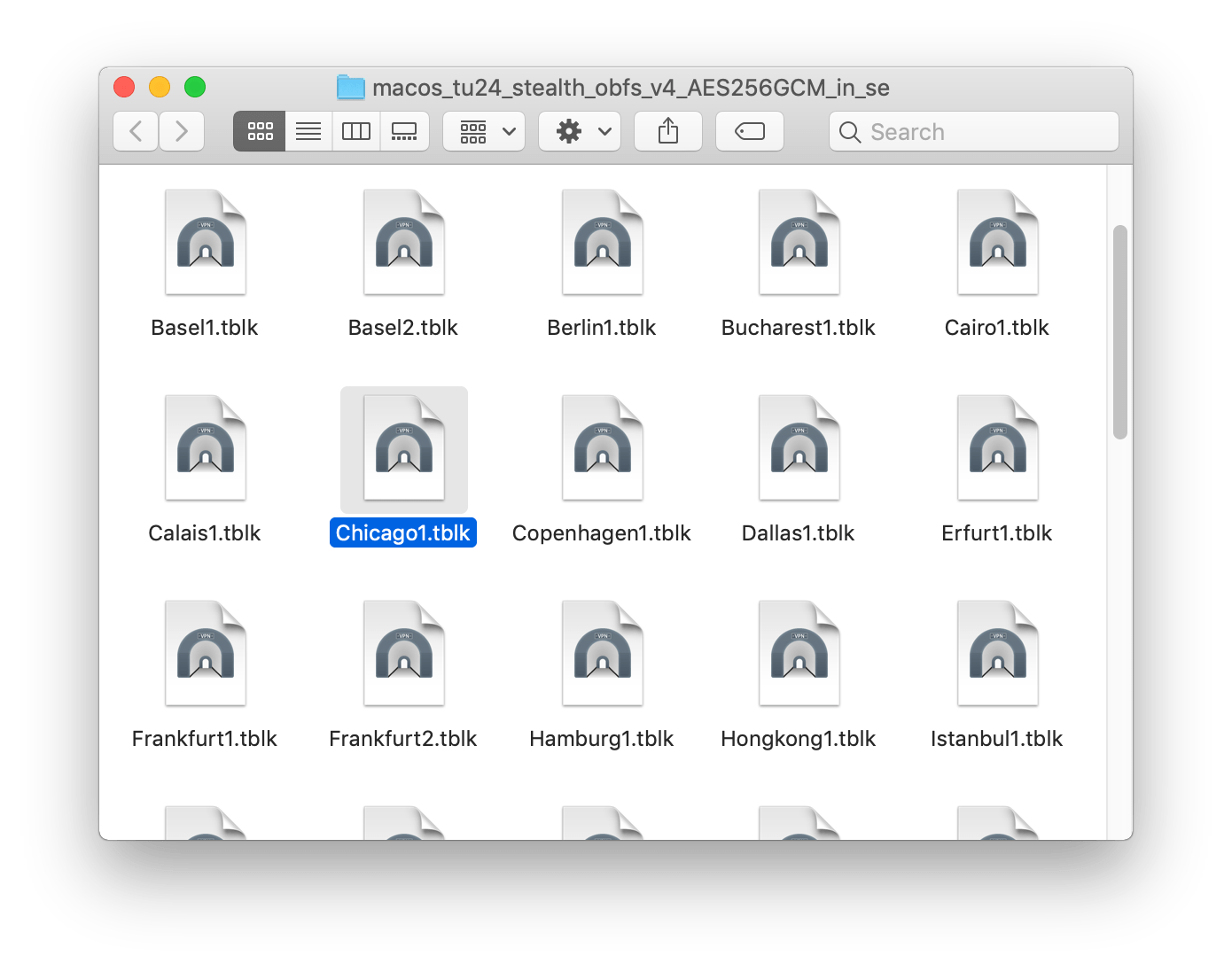
Download the Tunnelblick profiles
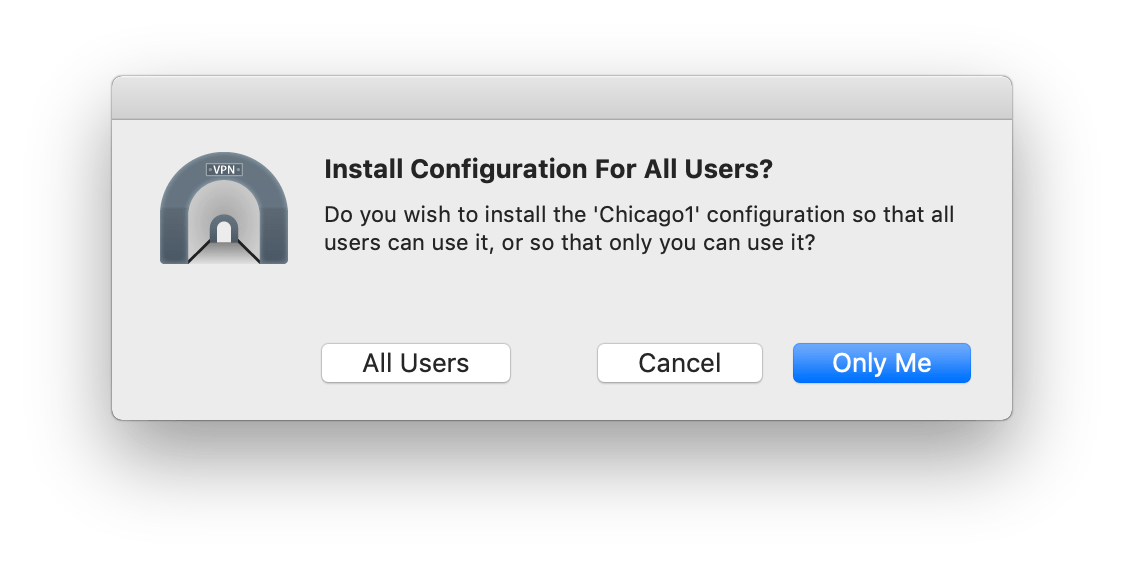
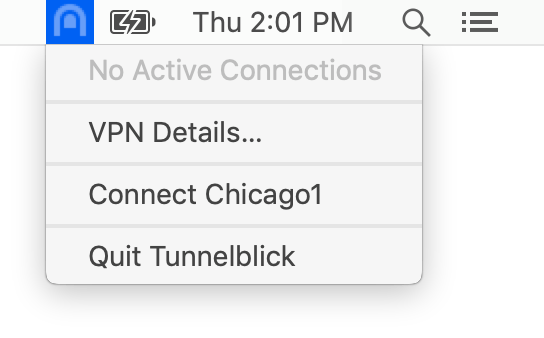
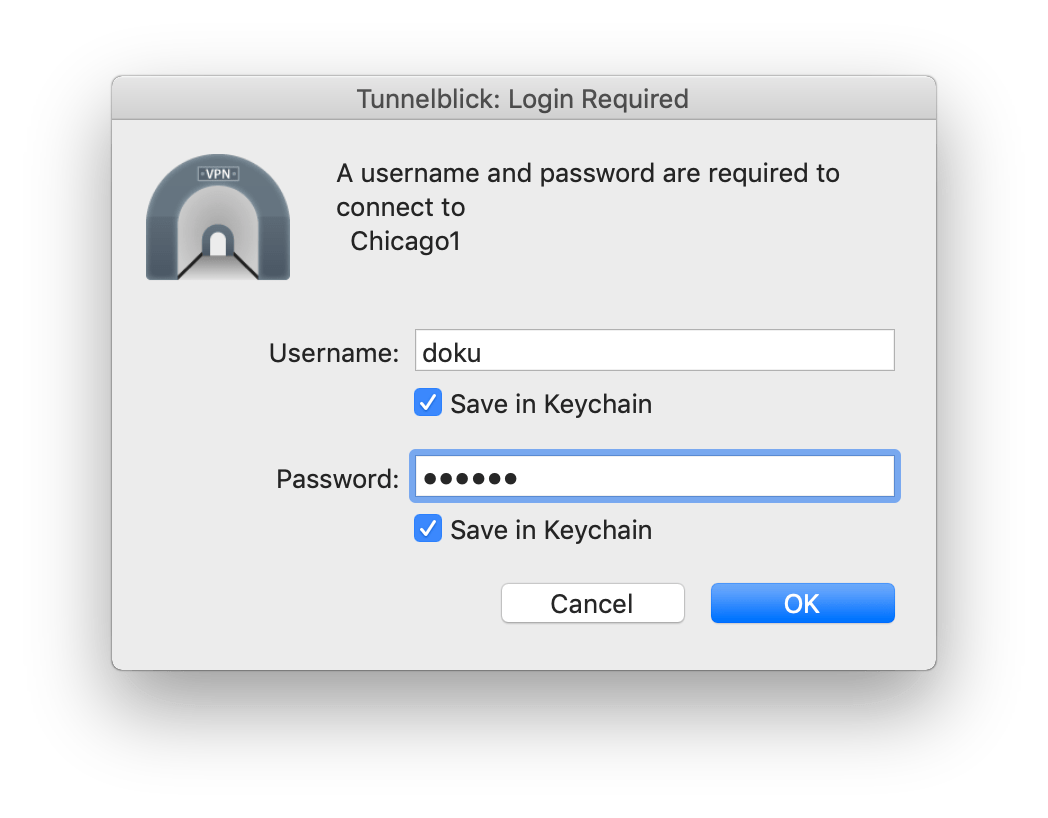
Download all necessary Tunnelblick profiles (OpenVPN) as a ZIP file. These are already preconfigured for use with obfsproxy.
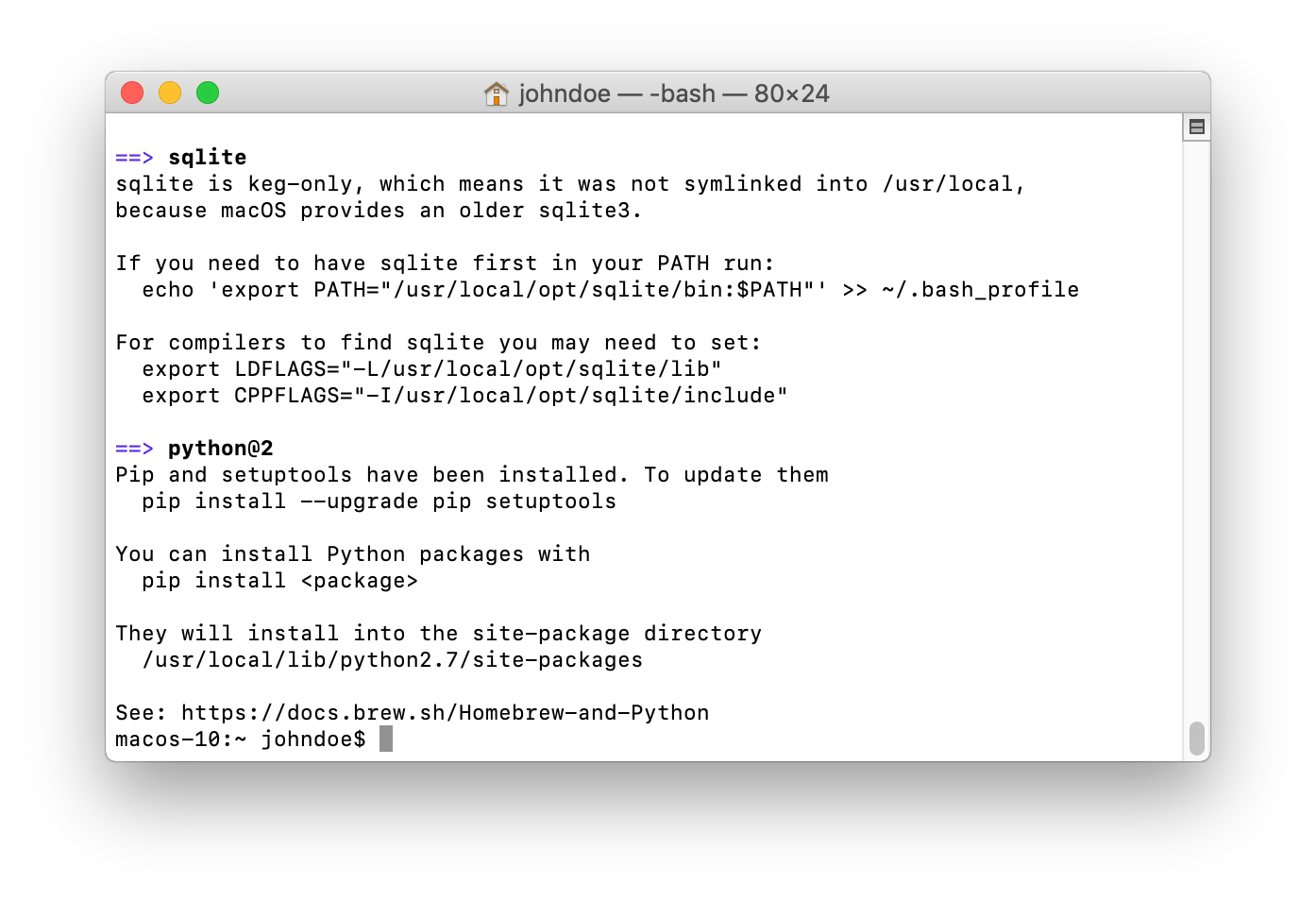
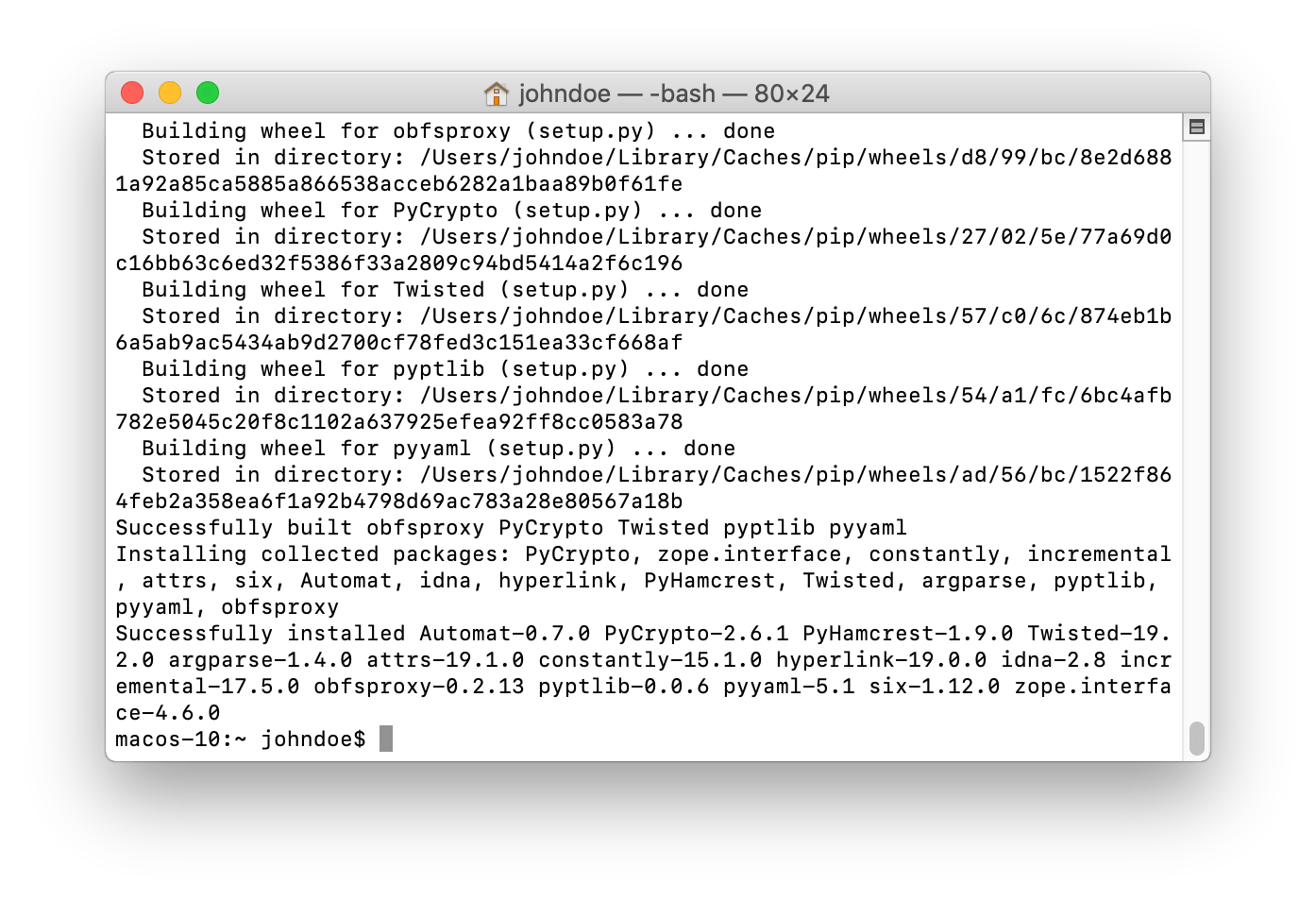
Download View alternate downloadsInstall obfsproxy
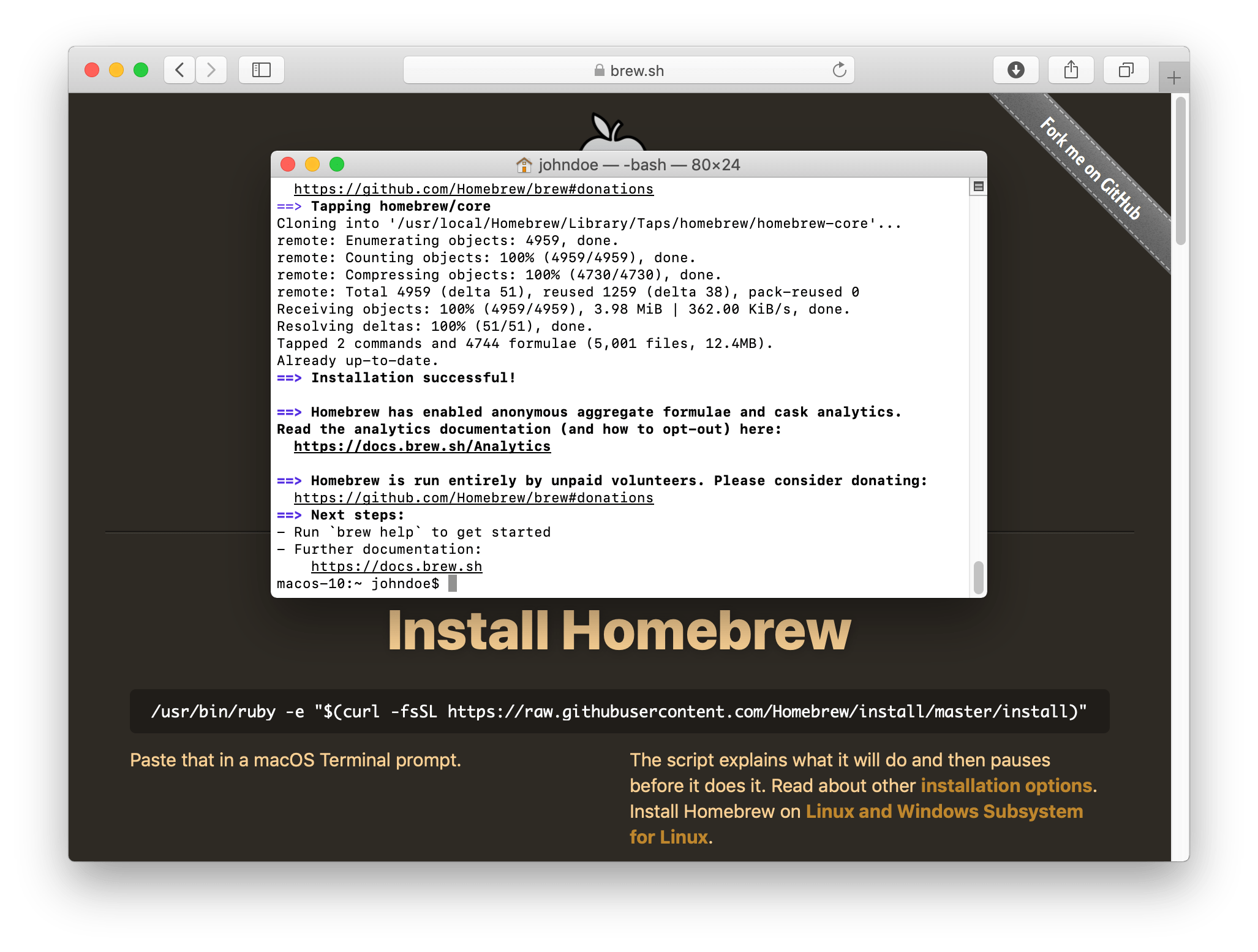
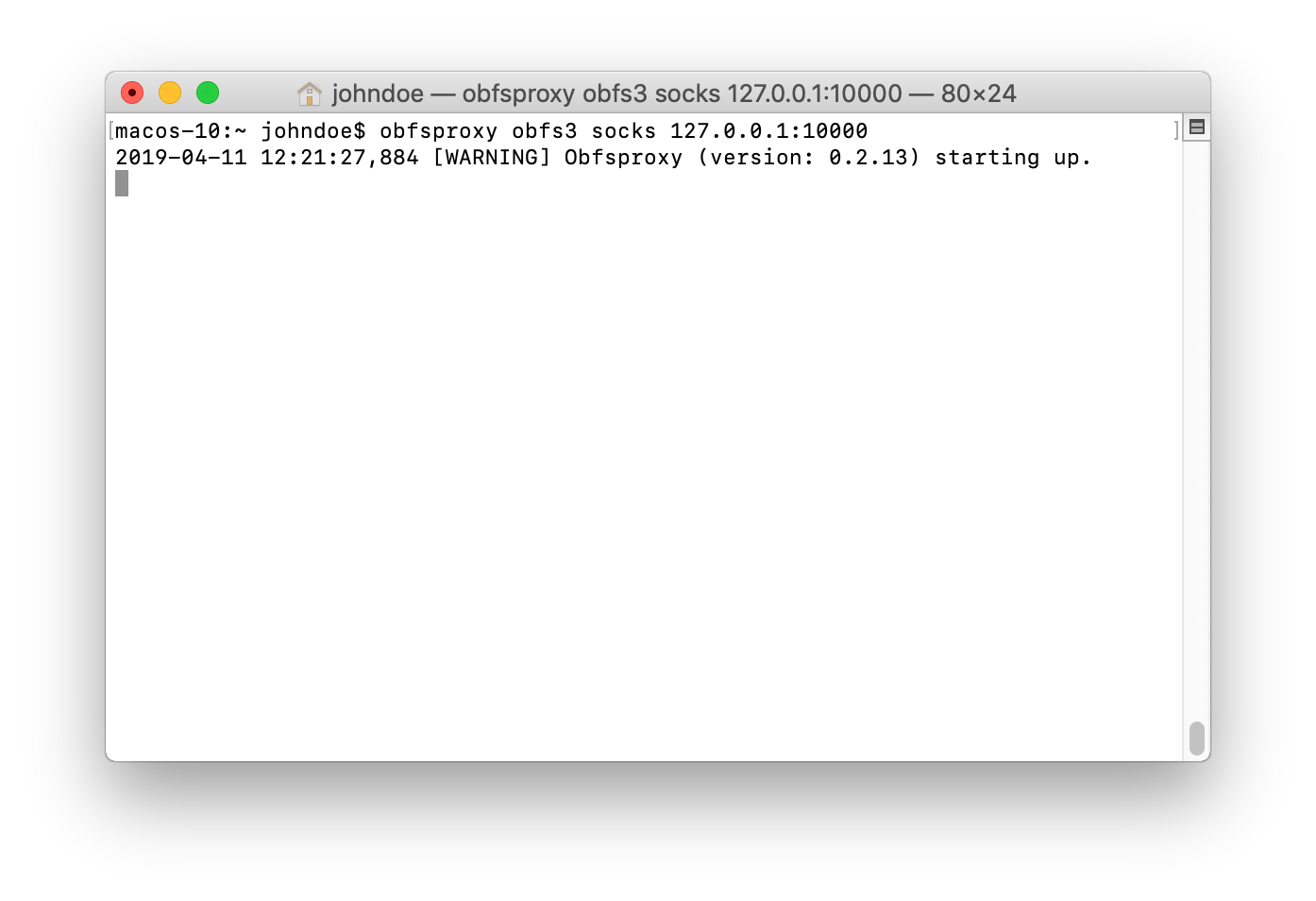
To install obfsproxy you first need the software package management Homebrew.
Open a terminal and install Homebrew according to the installation instructions on the Homebrew website.
Installing Homebrew will take a while.
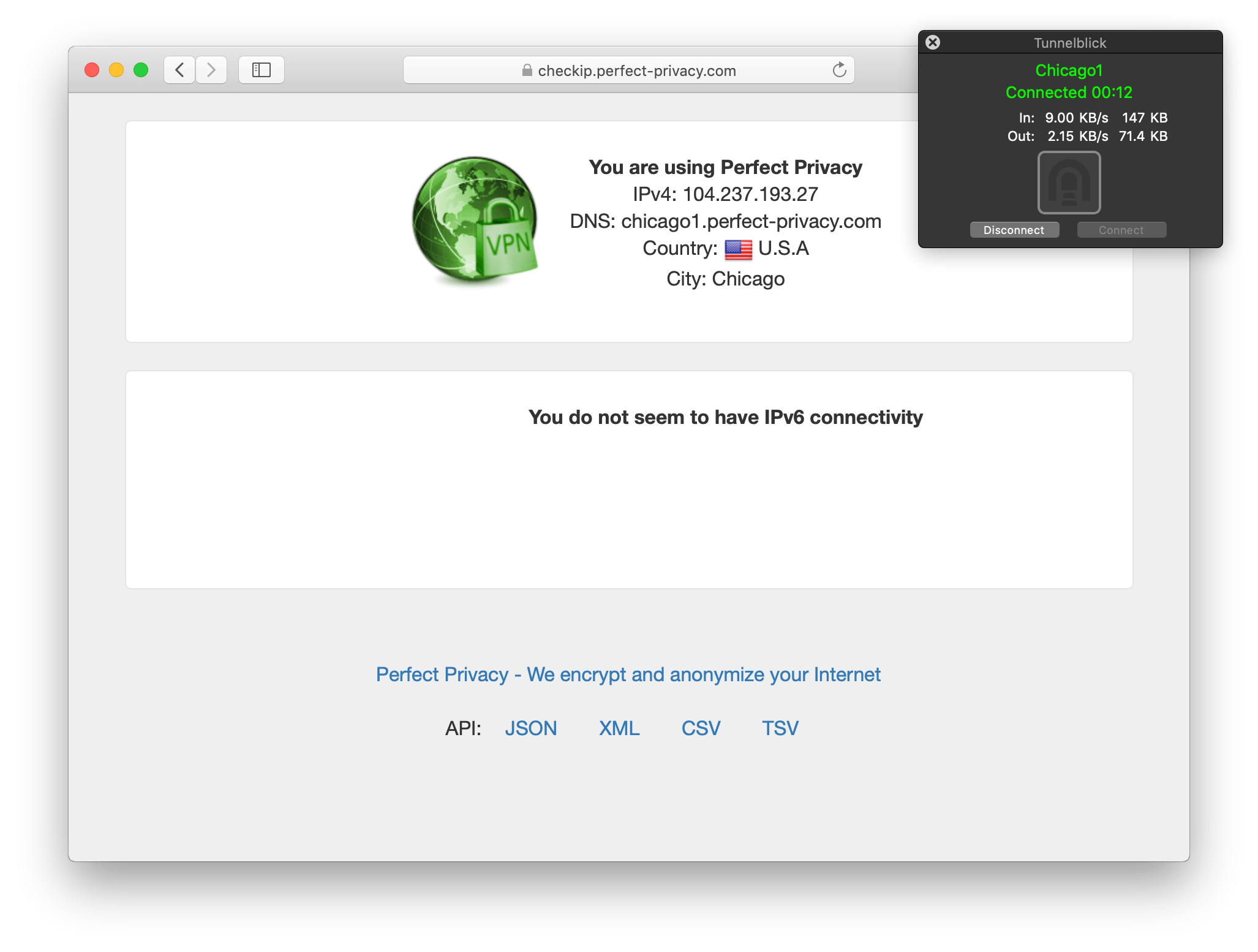
Check that the VPN connection is working correctly by going to the Check-IP web page.

Questions?
If you have any questions, comments or other feedback regarding this tutorial, please use the corresponding thread in our community forums.