Please note:
AsusWRT Merlin is an alternative open source firmware for Asus routers. You will have to install this firmware manually on your router, and your warranty may be voided.
Follow this link if you want to set up VPN access on the default AsusWRT firmware instead.
Downloading the OpenVPN configuration files
Download the archive with OpenVPN configuration files and unpack it.
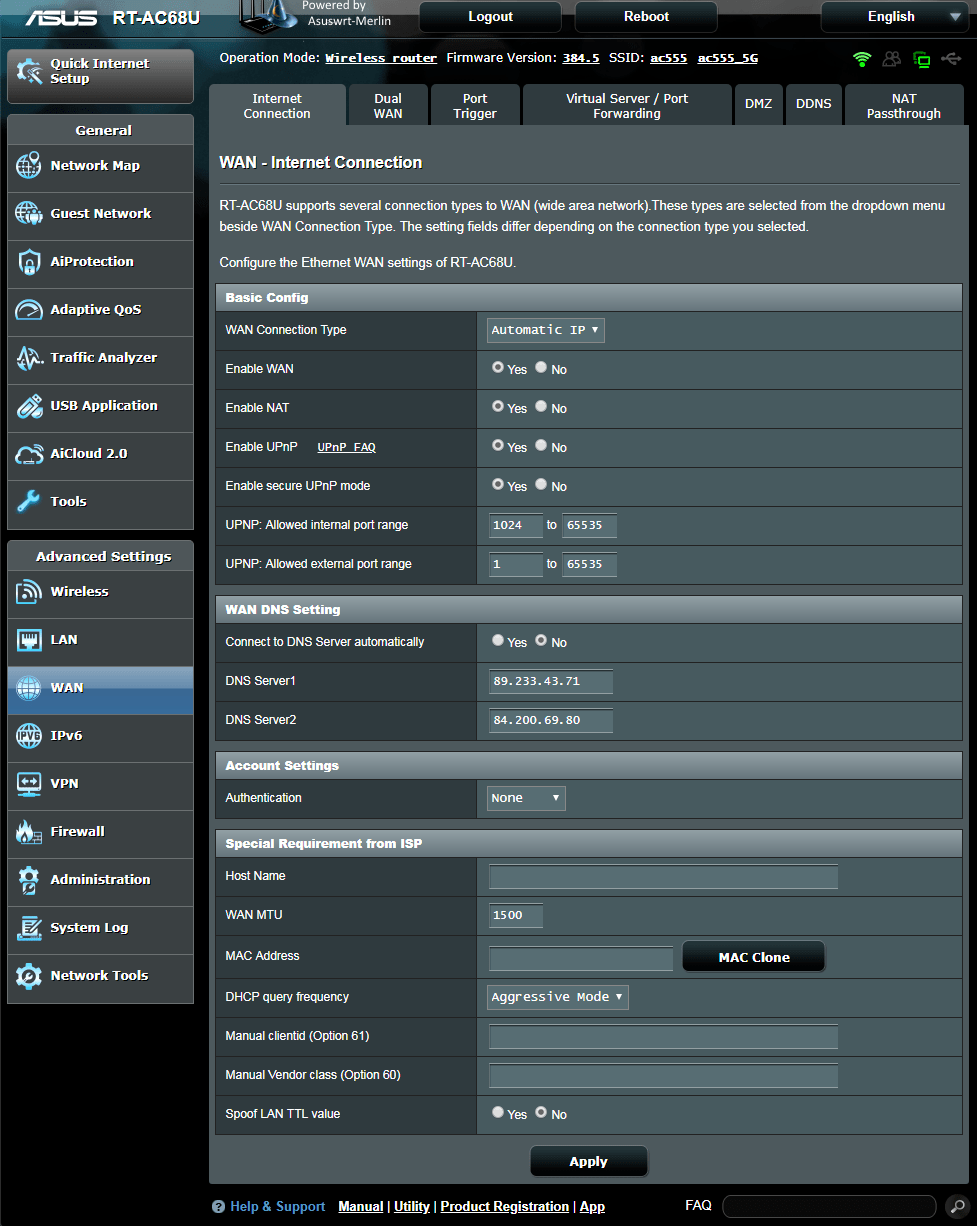
Download View alternate downloadsLog in to your router and under Advanced Settings → WAN → WAN DNS Settings set Connect to DNS Server automatically to No and enter at least two public DNS servers. You can either use Google’s DNS servers (8.8.8.8, 8.8.4.4) or any from the OpenNIC project.
Then click on Apply.
Note: If you want, you can also use Perfect Privacy DNS servers (you can find the IPs on the DNS server page in the customer area). Note that these DNS servers will only resolve *.perfect-privacy.com domains when VPN is not connected which means that Internet access will not work without the VPN being connected.
However, there will be no DNS leak when using public name servers instead, since all DNS requests will be sent anonymized through the VPN tunnel while a VPN connection is established.
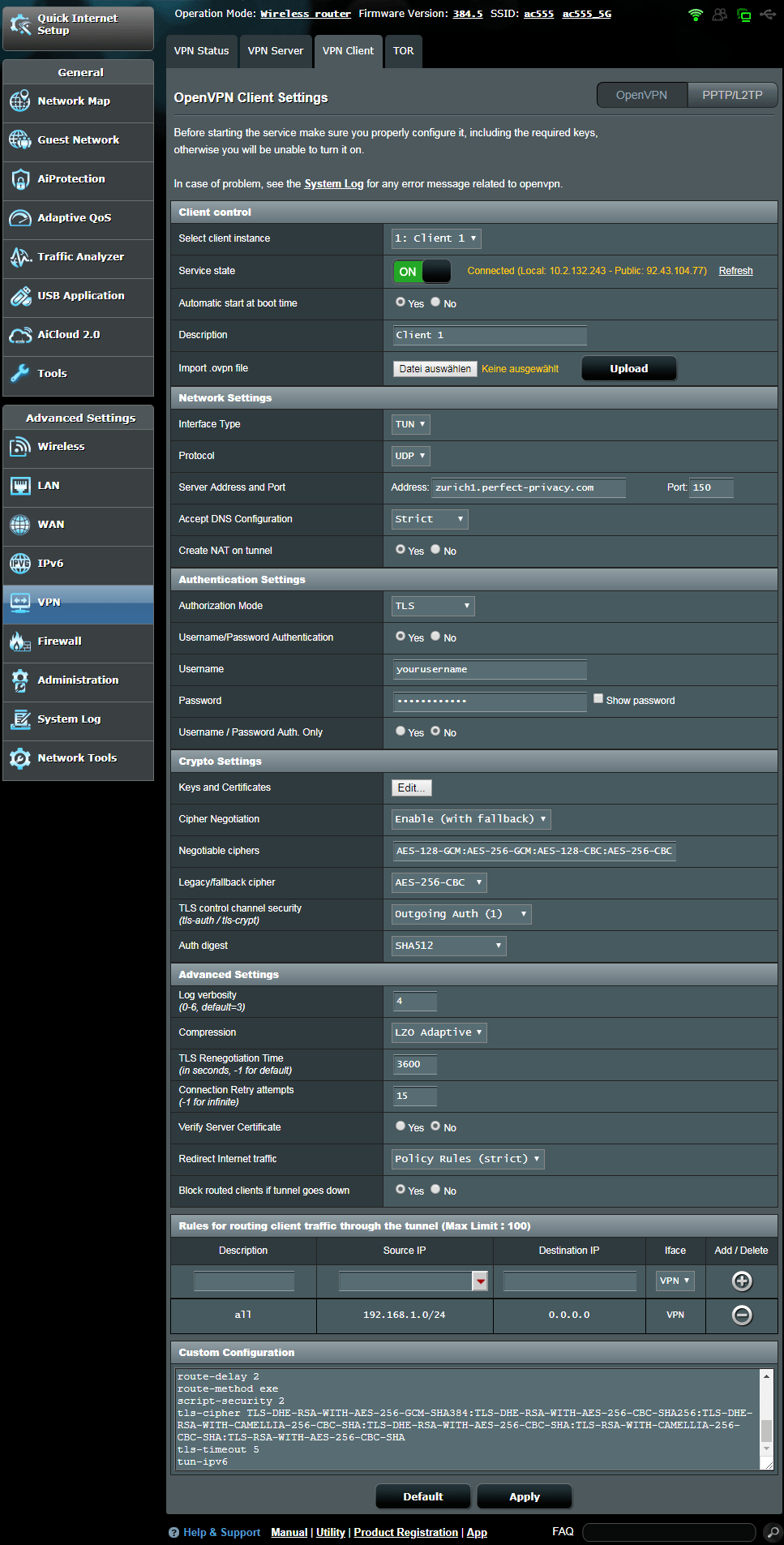
Navigate to Advanced Settings → VPN and click on the VPN Client tab. Next to Import .ovpn file click on Choose file and select one of the .ovpn files from the previously downloaded archive with configurations (see top of this guide). In this documentation we use Zurich.ovpn
Under Client control set Automatic start at boot time to Yes. (This will ensure that the OpenVPN connection will be established after restarting the router). Configure the rest of the settings as follows:
- Accept DNS Configuration:
Exclusive - Username:
Your Perfect Privacy username - Password:
Your Perfect Privacy password - Cipher Negotiation:
Enable with Password - Compression:
LZO Adaptive - Redirect Internet traffic:
Policy Rules (strict) . (On older Merlin firmware versions use Policy Rules). - Block routed clients if tunnel goes down:
Yes (Kill-Switch)
Under Rules for routing client traffic through the tunnel enter the following:
- Description:
all - Source IP:
192.168.1.0./24 - Iface:
VPN
Then click on the + icon below Add/Delete.
Remove the line
register-dnsClick on Apply and at the top switch the Service State to ON.
OpenVPN should now be connected. But you should restart your router to make sure OpenVPN will work correctly after a reboot.
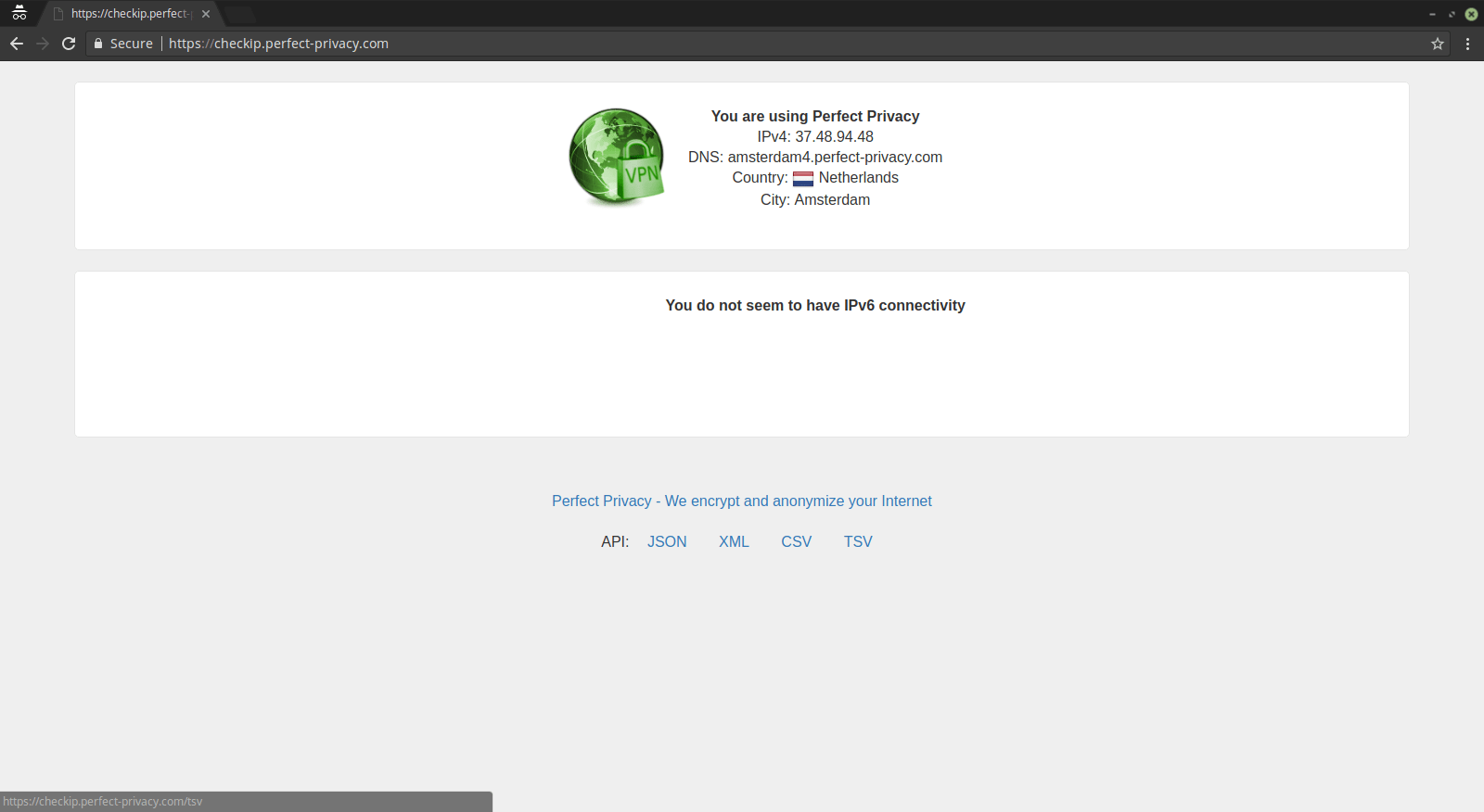
You can check that the VPN connection is working correctly by visiting our Check IP website from any device connected to the router.
Optional: Using port forwarding
Who wants to use one of the offered port forwarding methods, has to take into account that the forwarded ports are now arriving on the router. Simply always where the VPN tunnel exists. If you want to forward a port from the router to a device located in the LAN you have to use the following script to adjust the routing, because port forwardings created using the routers web GUI are only effective for the regular WAN adapter and completely ignore packets arriving on the network adapter of the VPN tunnel.
The command to create the script has to be executed on the router using SSH access. It has to be updated each time the port of the port forwarding changes! The command contains two placeholders for variable values which have to be replaced accordingly: YOURPORT with the port of the port forwarding, and THECOMPUTERSIP with the ip address of the device in the LAN to which the data arriving via the port forwarding should be forwarded. echo -e "#!/bin/sh \niptables -t nat -A PREROUTING -i tun+ -p udp --dport YOURPORT -j DNAT --to-destination THECOMPUTERSIP \niptables -t nat -A PREROUTING -i tun+ -p tcp --dport YOURPORT -j DNAT --to-destination THECOMPUTERSIP" > /jffs/scripts/nat-start && chmod +x /jffs/scripts/nat-start
To have the created script forward tcp and udp packets arriving for example on port 35000 to the local IP address 192.168.0.2 the command reads: echo -e "#!/bin/sh \niptables -t nat -A PREROUTING -i tun+ -p udp --dport 35000 -j DNAT --to-destination 192.168.0.2 \niptables -t nat -A PREROUTING -i tun+ -p tcp --dport 35000 -j DNAT --to-destination 192.168.0.2" > /jffs/scripts/nat-start && chmod +x /jffs/scripts/nat-start
Further information on the topic port forwarding can be found on the port forwarding page. The FAQ page contains answers to the most common questions on port forwarding.

Questions?
If you have any questions, comments or other feedback regarding this tutorial, please use the corresponding thread in our community forums.