If you cannot connect with OpenVPN, you are probably on a network that blocks VPN connections. With Stealth VPN, you still have the ability to break out of such networks.
With the help of these step by step guide you can establish an OpenVPN connection which is obfuscated using SSH.
You will need the following software:
- openvpn - for the VPN connection
- ssh - to hide the OpenVPN connection
- resolvconf - to avoid DNS leaks
- wget - to download VPN profiles and check the connection
- unzip - to unzip the VPN profiles
In the example we use Ubuntu 18.04, where the necessary packages have to be installed as follows:
sudo apt update && sudo apt install openvpn resolvconf
Download OpenVPN profiles
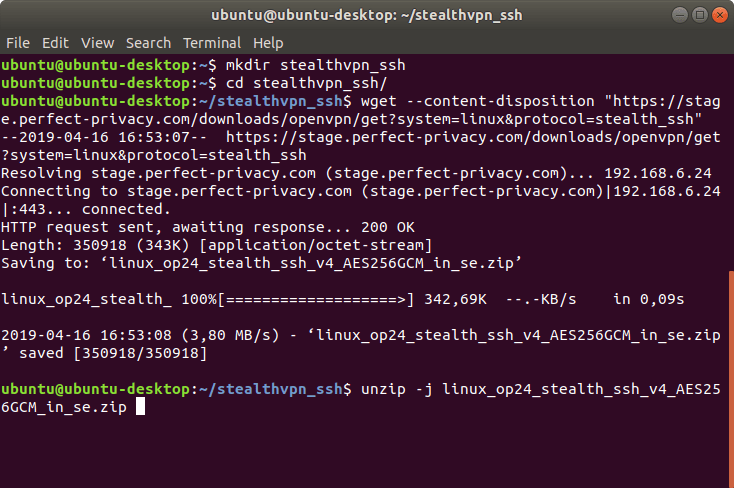
First download the OpenVPN profiles for use with SSH and extract it. We will create a new directory for this.
mkdir stealthvpn_ssh
cd stealthvpn_ssh
wget --content-disposition "https://www.perfect-privacy.com/downloads/openvpn/get?system=linux&protocol=stealth_ssh"
unzip -j linux_op24_stealth_ssh_v4_AES256GCM_AU_in_se.zip
If you have special requirements, you can download OpenVPN configurations with advanced options in the download area.
Start SSH
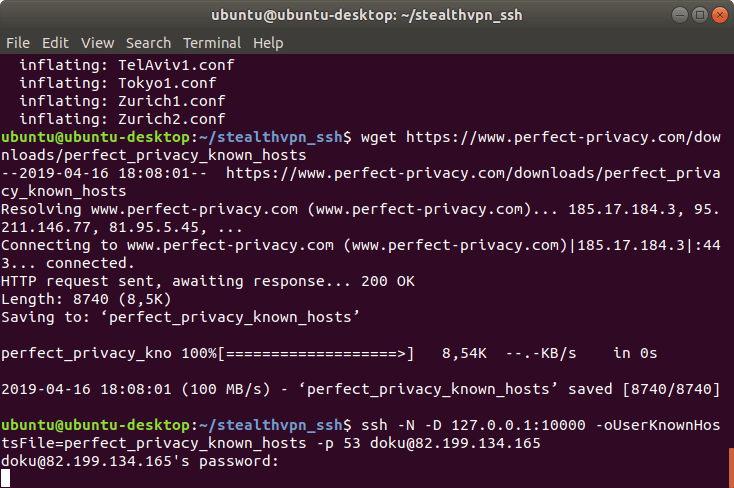
For SSH to verify the connection, the known_hosts file is required. Download it as follows:
wget https://www.perfect-privacy.com/downloads/perfect_privacy_known_hosts
The OpenVPN profile expects the SSH tunnel as a SOCKS proxy on local port 10000, so start SSH as follows:
ssh -N -D 127.0.0.1:10000 -oUserKnownHostsFile=perfect_privacy_known_hosts -p 53 USER_NAME@IP_ADDRESS
Instead of IP_ADDRESS, use the IP address of the desired server. This can be found on the OpenVPN with Stealth VPN (SSH) overview page.
Our tip: Choose a location that is geographically as close as possible to achieve the best speed.
Instead of USER_NAME, enter your Perfect Privacy username here.
For the port you can choose between 22, 53, 443, 8085, 9009 or 36315. Ports 53 and 443 are particularly recommended to bypass VPN blocking (in the example, we chose port 53).
If you run the program by pressing Enter, you will be asked for your Perfect Privacy password. Enter this and confirm with Enter.
Start OpenVPN
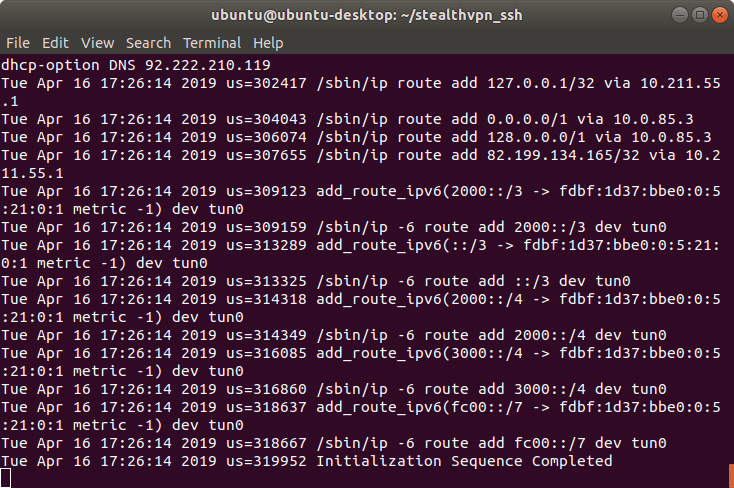
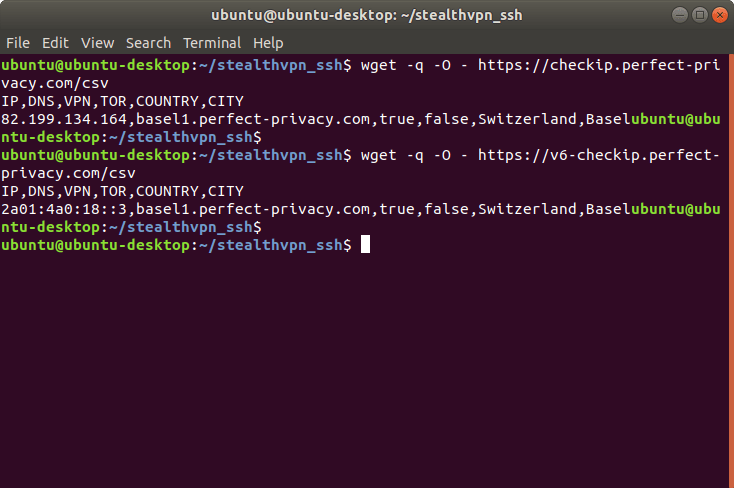
Now you can start OpenVPN in a new terminal:
sudo openvpn VPN_PROFILE
Instead of VPN_PROFILE, use a configuration file of your choice (file extension .conf). In the example we use Basel1.conf.
Our tip: Choose a location that is geographically as close as possible to achieve the best speed.

Questions?
If you have any questions, comments or other feedback regarding this tutorial, please use the corresponding thread in our community forums.