New features: Obfuscation & Cipher Negotiation
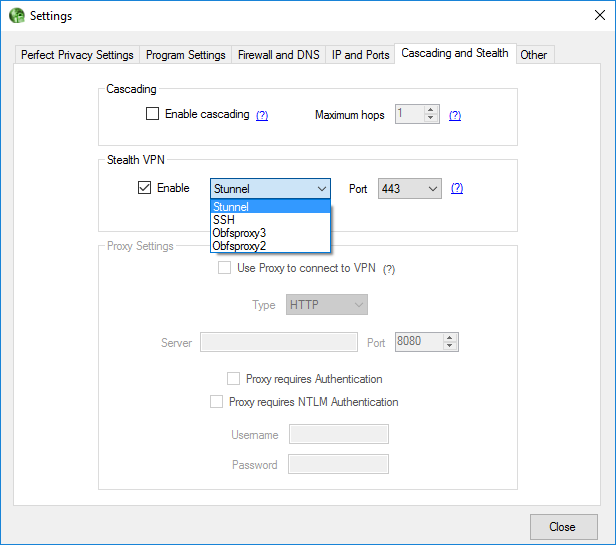
With our latest client update we offer two new features. Firstly, you can now obfuscate your VPN traffic by tunneling it through stunnel, ssh or obfsproxy2/obfsproxy3. You can also choose to use the ports 22 (SSH), 53 (DNS) and 443 (SSL). Collectively we call these obfuscation methods our Stealth VPN feature, which is now built into the Windows client where you can select these options with a simple mouse click. You can also use the obfuscation manually with OpenVPN on Linux and Mac.
Why obfuscation?
With obfuscation it is possible to use VPN in locations where network connections are restricted, for instance in schools, universities, workplace or public hotspots. And it is helpful in countries that either restrict traffic or outright block normal VPN connections, for instance Turkey, China, Iran, Saudi Arabia and the United Arab Emirates (UAE). The ports 22, 53 and 443 are usually not restricted because they are essential for basic Internet functionality.
Obfuscation can also increase your download speed: Some ISPs throttle the traffic on certain ports to save bandwidth – using a tunnel through SSH or obfsproxy can get around that.
You can find more information about the Stealth VPN feature on our Stealth-VPN page. If you want to use obfuscation with Linux, we provide documentation for doing this over SSH, stunnel and obfsproxy.
What is cipher negotiation?
The second new feature is cipher negotiation which was introduced in the recently released OpenVPN 2.4 version. This allows you to manually choose the encryption cipher to use in OpenVPN. This can be useful for some embedded devices that don’t have much CPU power (for instance a Raspberry Pi). Normally, AES-256 is being used but with cipher negotiation you can for instance choose AES-128 or a completely different cipher not based on AES like Camellia. This will result in better performance. Additionally, in many cases the main reason for using the VPN is anonymity while the encryption of the traffic is not that relevant (streaming, downloading, etc.).